Cybersecurity is an important concern for individuals and organizations alike. It involves protecting against threats such as hacking, phishing, and malware, and ensuring the confidentiality, integrity, and availability of data and systems.
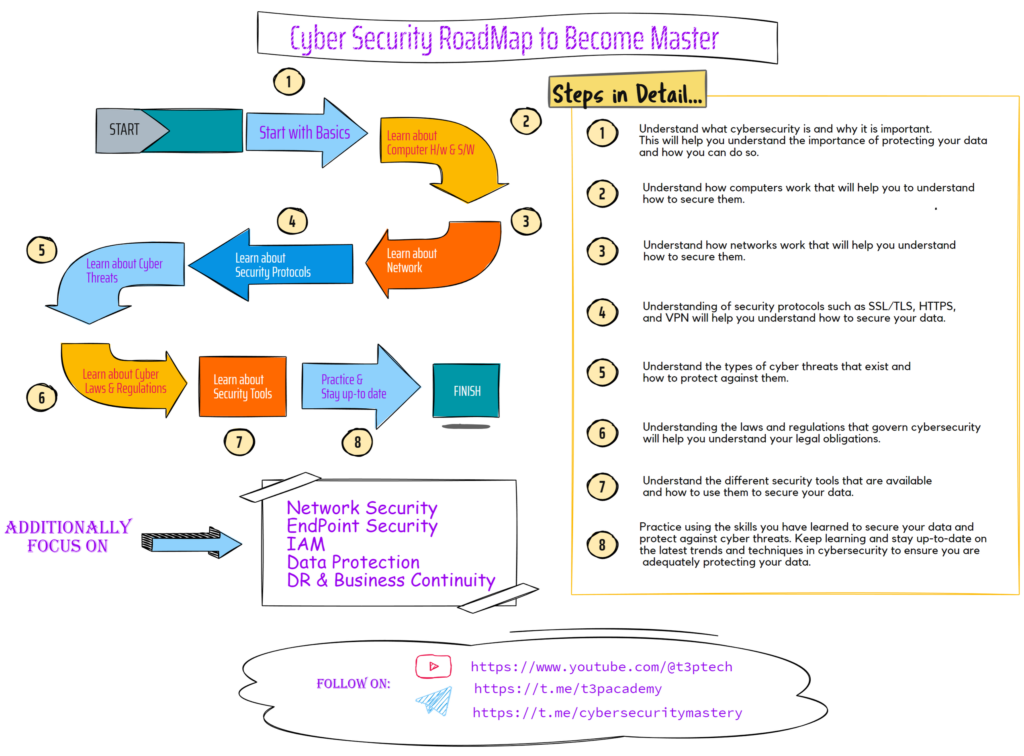
If you’re looking to develop a cybersecurity roadmap, here are some steps you might consider taking:
💥Start with the basics:
Understand what cybersecurity is and why it is important. This will help you understand the importance of protecting your data and how you can do so.
💥 Learn about computer hardware and software:
Understanding how computers work will help you understand how to secure them.
💥 Learn about networks:
Understanding how networks work will help you understand how to secure them.
💥 Learn about security protocols:
Understanding security protocols such as SSL/TLS, HTTPS, and VPN will help you understand how to secure your data.
💥 Learn about cyber threats:
Understand the types of cyber threats that exist and how to protect against them.
💥 Learn about cyber laws and regulations:
Understanding the laws and regulations that govern cybersecurity will help you understand your legal obligations.
💥 Learn about security tools:
Understand the different security tools that are available and how to use them to secure your data.
💥 Practice:
Practice using the skills you have learned to secure your data and protect against cyber threats.
💥 Stay up-to-date:
Keep learning and stay up-to-date on the latest trends and techniques in cybersecurity to ensure you are adequately protecting your data.
Some things you might include in your cybersecurity roadmap include:
💥 Network security:
This involves protecting your network and systems from threats such as hacking, malware, and unauthorized access.
💥 Endpoint security:
This involves protecting devices such as computers, laptops, and mobile phones from threats.
💥 Identity and access management:
This involves controlling who has access to your systems and data, and ensuring that only authorized users can access them.
💥 Data protection:
This involves protecting your data from threats such as data breaches, theft, and loss.
💥 Disaster recovery and business continuity:
This involves having plans in place to ensure that you can recover from a cyber attack or other disaster and continue to operate.
🤝Like & share this post for better reach & help others.🤝